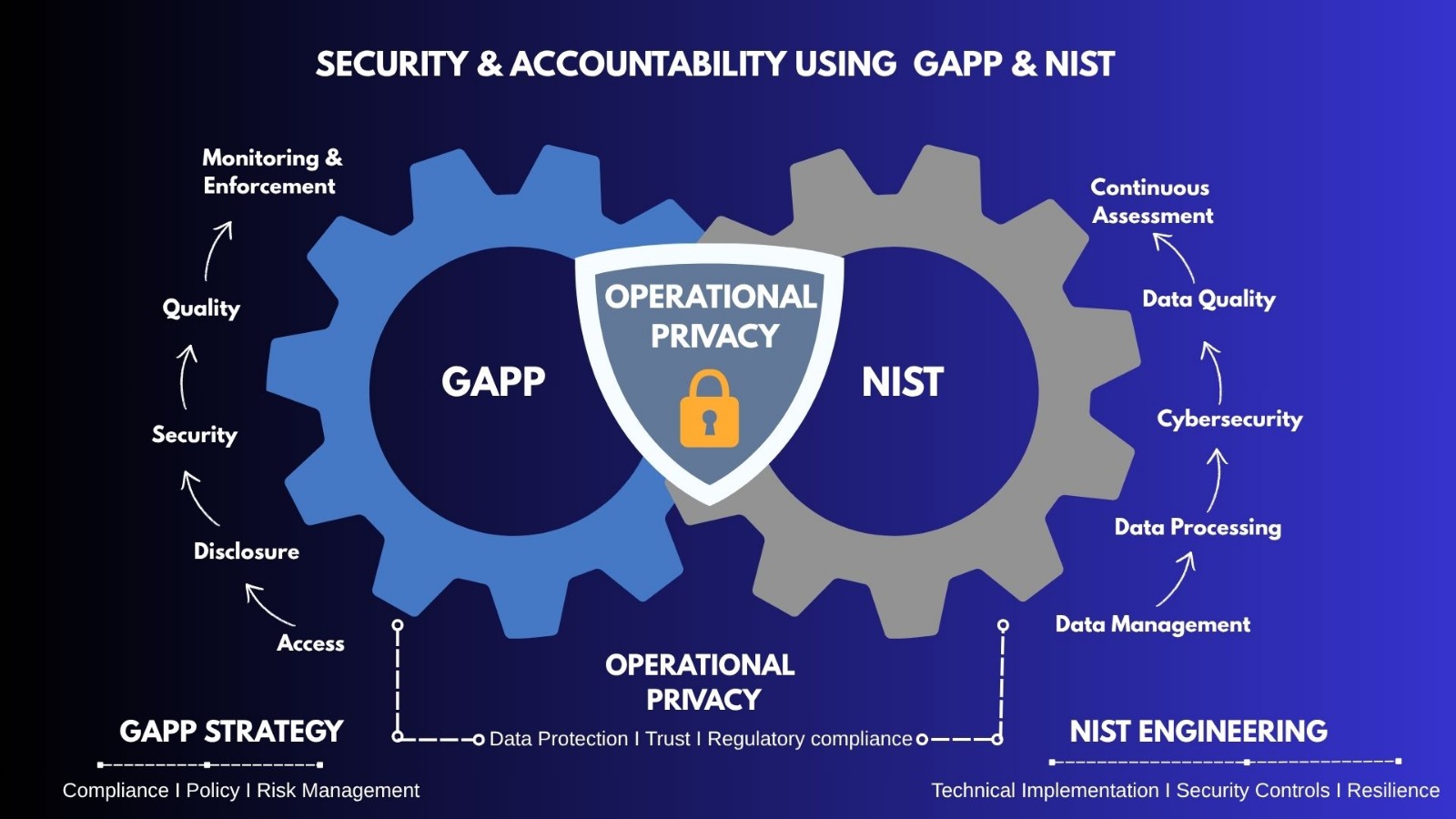
GAPP and NIST Synergies
Operationalizing Privacy and Accountability with GAPP & NIST — (Part 2)
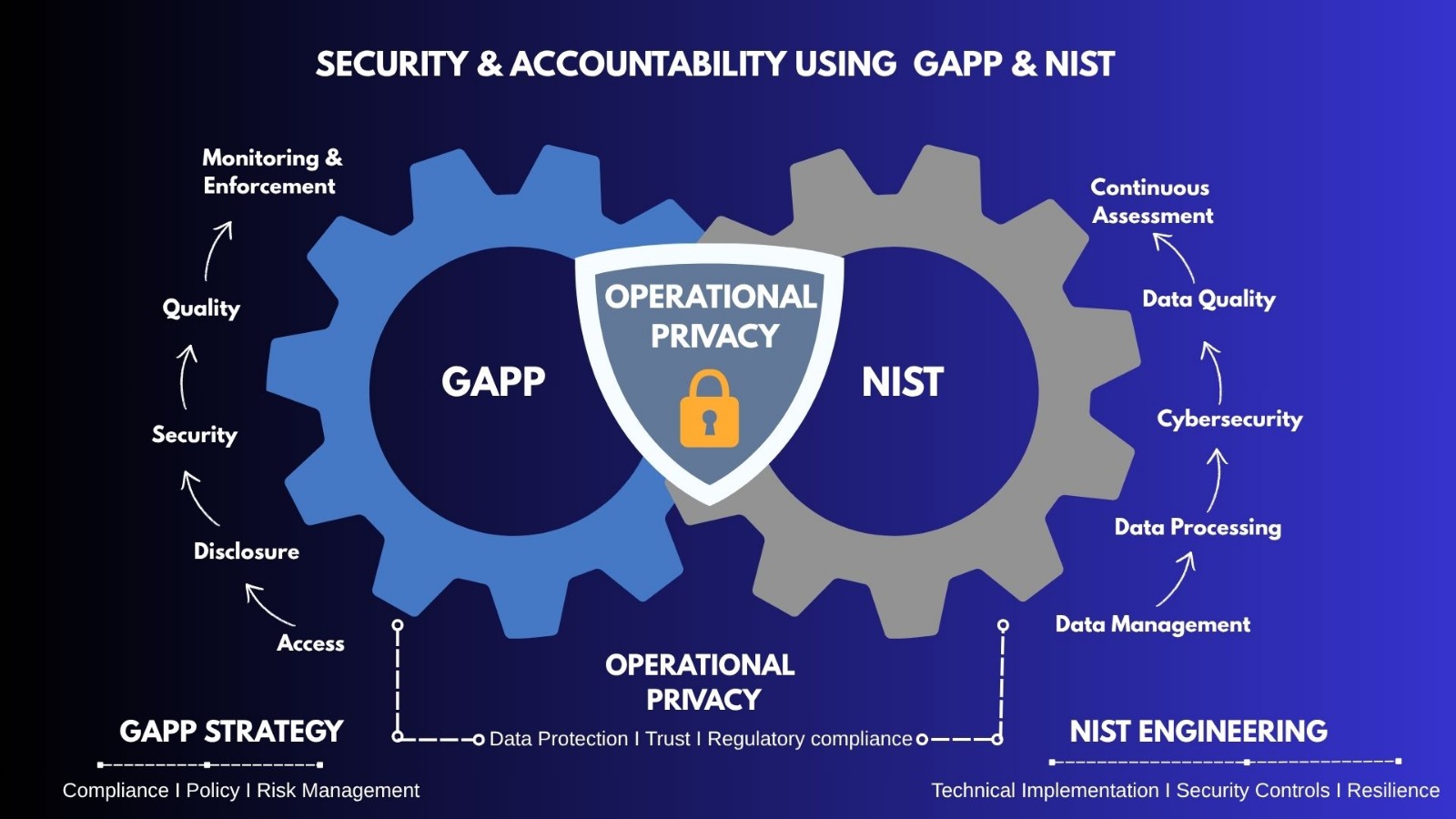
GAPP and NIST Synergies
In Part 1 of this series, we explored how to "hardcode" privacy into the internal lifecycle of an Antivirus (AV) product—from the initial management of data to its eventual secure disposal using NIST 800-88 standards. We demonstrated that operationalizing privacy is not about writing better policies, but about building better architectures.
However, a privacy program is only as strong as its weakest external link. An AV product does not exist in a vacuum; it constantly communicates with users, shares threat intelligence with global partners, and must defend itself against an evolving landscape of cyber threats.
In this second and final installment, we move beyond the internal database to explore the "outside world." We will look at how to solve the Identity-Telemetry Paradox in user access, how to implement "Privacy Gates" for third-party disclosures, and how to use the NIST Cybersecurity Framework to ensure that "Security for Privacy" is an automated, audit-ready reality.
Challenge (The Identity–Telemetry Gap): Under GAPP Principle 6 (Access), individuals have the right to obtain their personal data. In a typical anti-virus (AV) architecture, however, user profile data (such as name, email, or billing details) is deliberately kept separate from technical telemetry (such as file hashes or behavioural logs). This separation is a good security practice because it reduces the risk that telemetry data can be directly linked back to an individual in the event of a breach.
The difficulty is that this same design makes access requests harder to fulfill. If telemetry data is not directly tied to an identifiable user, how can the organization provide access without re-linking those datasets and increasing privacy risk?
Goal (In-App, Controlled Access Without Re-Identification): To meet GAPP Principle 6, the organization needs to provide access while still preserving the benefits of data separation. The practical solution is to shift from manual, identity-based requests (such as email requests) to an in-product access mechanism. Instead of relying on personal identifiers, the system can use a device-level identifier (such as a UUID) to retrieve relevant data.
From a NIST perspective:
This approach allows the organization to fulfill access rights without unnecessarily re-identifying or centralizing user data.
NIST CT.DM-P1 (Data Processing for Access / Retrieval of Data): In line with GAPP access requirements and NIST governance controls, the user initiates the request directly within the application (e.g., “Request Privacy Report”). The request is authenticated using the device’s credentials (such as a device certificate), ensuring that only the legitimate user of that device can initiate the process.
Using NIST CT.DM-P1, an automated backend process retrieves the relevant telemetry data. Because the request is tied to the device identifier (UUID), the system does not need to query or reconnect with the user profile database. This preserves the original separation of datasets while still enabling access.
Before delivering the data, a processing layer applies (Sanitization) NIST CT.DP-P (Data Processing) to make the output understandable and appropriate. For example, internal technical indicators or detection rules are translated into user-friendly descriptions. This ensures transparency while also protecting proprietary detection methods.
Consistent with NIST CT.DM-P2, the final report is delivered through the secure application channel. The user is notified within the app and can download the report directly. By avoiding external channels such as email, the organization reduces the risk of unauthorized disclosure while still fulfilling the GAPP Principle 6 requirement of access.
Challenge: In practice, anti-virus companies routinely share suspicious files with third-party platforms (such as VirusTotal or partner labs) to support threat intelligence. However, these files can contain personal data—either in metadata (e.g., author name, company, file path) or within the content itself. Without proper controls, this creates a clear gap between the intent and actual practice. What is meant to be a security-driven disclosure can unintentionally become a privacy breach.
Goal: To align with GAPP Principle 7, the organization must ensure that only necessary and appropriate information is disclosed to third parties. This means introducing a control layer that filters and minimizes personal data before any external sharing occurs.
From a NIST perspective, this maps to:
Together, GAPP defines the requirement (controlled disclosure), while NIST provides the mechanisms to enforce it.
NIST GV.PO-P (Governance policies, processes, and procedures for privacy): All external data sharing must follow defined policy controls. Practically, this means any file flagged for external submission is automatically routed to a controlled sanitization environment, rather than being shared directly.
NIST CT.DP-P (Data Processing): The organization implements automated scanning to identify personal data within files. Tools such as NLP-based systems (e.g., spaCy) can detect names, email addresses, or system-specific identifiers. This step operationalizes GAPP’s requirement to assess what is being disclosed before it leaves the organization.
The Redaction: To enforce data minimization within GAPP Principle 7, different handling rules are applied:
This ensures that disclosure is proportionate and limited, as required by GAPP.
The Audit Trail: Finally, in line with GAPP accountability requirements and NIST GV.MT-P (Monitoring and Tracking), every disclosure is logged, including what sanitization steps were applied.
Challenge: Under GAPP Principle 8 (Security for Privacy), organizations must protect personal data through appropriate safeguards. In the case of an antivirus (AV) product, this requirement becomes especially important. AV software operates with very high privileges—it can monitor files, processes, and network activity across the system. As a result, the backend systems that store this telemetry become a highly sensitive aggregation point.
If components such as the telemetry store or the privacy access interface (as described in Principle 6) are compromised, an attacker could gain extensive visibility into user environments, potentially linked to device identifiers. In this context, security failures directly translate into privacy risks.
Goal (Strengthening the Privacy Infrastructure): o meet GAPP Principle 8, the organization must ensure that personal data is protected through strong, enforceable technical measures—not just policies. A practical way to approach this is by adopting a zero trust mindset, where no system or request is automatically trusted, even if it originates internally.
From a NIST perspective, this aligns with the Protect and Detect components of NIST Cybersecurity Framework:
Here, GAPP defines the requirement for security, while NIST CSF provides the structure for implementing and validating those protections.
NIST PR.AA (Identity Management and Access Control): All communication between the AV client and backend systems should be authenticated using strong mechanisms such as mutual TLS (mTLS). This ensures that only legitimate, verified installations can interact with the backend, reducing the risk of unauthorized data access or injection.
NIST PR.DS (Data Security): Telemetry data should be encrypted both in transit and at rest. For example, using AES-256 encryption with secure key management (e.g., TPM-backed storage) helps ensure that even if storage systems are accessed, the data remains protected. This directly supports GAPP’s requirement to safeguard personal data against unauthorized access.
NIST DE.AE (Anomalies and Events): To complement preventive controls, NIST DE.AE focuses on detection. For instance, monitoring the privacy access interface for unusual patterns—such as a sudden spike in data requests across multiple device IDs—can help identify potential misuse or compromise. In such cases, automated responses (e.g., temporarily blocking requests and alerting the security team) can limit exposure and support rapid incident response.
Challenge (The Scrubbing vs Detection Trade-off): Under GAPP Principle 9 (Quality), organizations must ensure that personal data is accurate, complete, and relevant for its intended use. In an antivirus (AV) context, this creates a practical tension. To protect privacy, malware samples are often sanitized before being shared or processed. However, if this sanitization alters the file too much—such as removing key behavioural indicators—the effectiveness of the detection engine may be reduced.
At the same time, poor-quality data can also create problems. For example, relying on outdated or inaccurate threat intelligence (such as an incorrect IP blacklist) could result in legitimate user activity being blocked. In both cases, the issue is not just technical—it reflects a failure to maintain data quality.
Goal (Maintaining Data Quality Without Undermining Privacy): To meet GAPP Principle 9, the organization needs to ensure that privacy controls do not unintentionally reduce the usefulness or accuracy of the data being processed. This means:
NIST CT.DP-P3 (Data Processing – Data Quality): When a file is processed for privacy purposes, both the original and sanitized versions can be retained within a controlled environment for comparison. This allows the system to assess whether the sanitization process has affected the file’s analytical value.
Using automated checks aligned with NIST CT.DP-P3, the AV engine is run on both versions of the file. If the original file is correctly identified as malicious but the sanitized version is not, this indicates that the privacy process may have removed important detection signals. Where such gaps are identified, the system flags them for review. This allows engineering teams to refine sanitization rules (for example, adjusting what types of strings or data elements should be excluded from redaction). This step ensures that privacy controls are continuously improved without compromising detection accuracy.
Challenge: Gaps in Ongoing Enforcement: Under GAPP Principle 10 (Monitoring and Enforcement), organizations are expected to ensure that privacy controls are not only implemented, but also actively monitored and enforced over time. In practice, many privacy controls operate in the background and may fail without immediate visibility. For example, a certificate validation check might be misconfigured during a system update, or a data-scrubbing component could stop functioning due to a dependency issue.
If such failures go unnoticed, the organization may continue operating under the assumption that controls are working as intended. This creates a risk where compliance gaps are only identified after an incident or external review, rather than being detected internally.
Goal (Continuous Monitoring and Verifiable Compliance): To meet GAPP Principle 10, the organization needs to move beyond periodic or manual checks and establish continuous oversight of its privacy controls. This involves:
NIST GV.CM-P (Continuous Monitoring) & ID.RA-P (Risk Assessment): Automated validation checks can be implemented to confirm that key privacy controls are working. For example, periodic test inputs (such as synthetic data containing mock personal information) can be passed through the data processing pipeline. If this data is not properly handled (e.g., not removed before external sharing), the system can trigger an alert and temporarily restrict further data flows until the issue is resolved.
Immutable Audit Logs (GV.CM-P): o support accountability under GAPP Principle 10, all significant privacy-related actions—such as access requests or data disclosures—should be logged. Using secure, tamper-resistant storage (e.g., write-once-read-many systems with cryptographic protections) helps ensure that these logs cannot be altered. This provides a reliable audit trail that can be used for internal reviews, incident investigations, or regulatory inquiries.