GAPP and NIST Synergies
Plan with GAPP. Build with NIST: A Practical Demonstration for AV Privacy Engineering — (Part 1)
GAPP and NIST Synergies
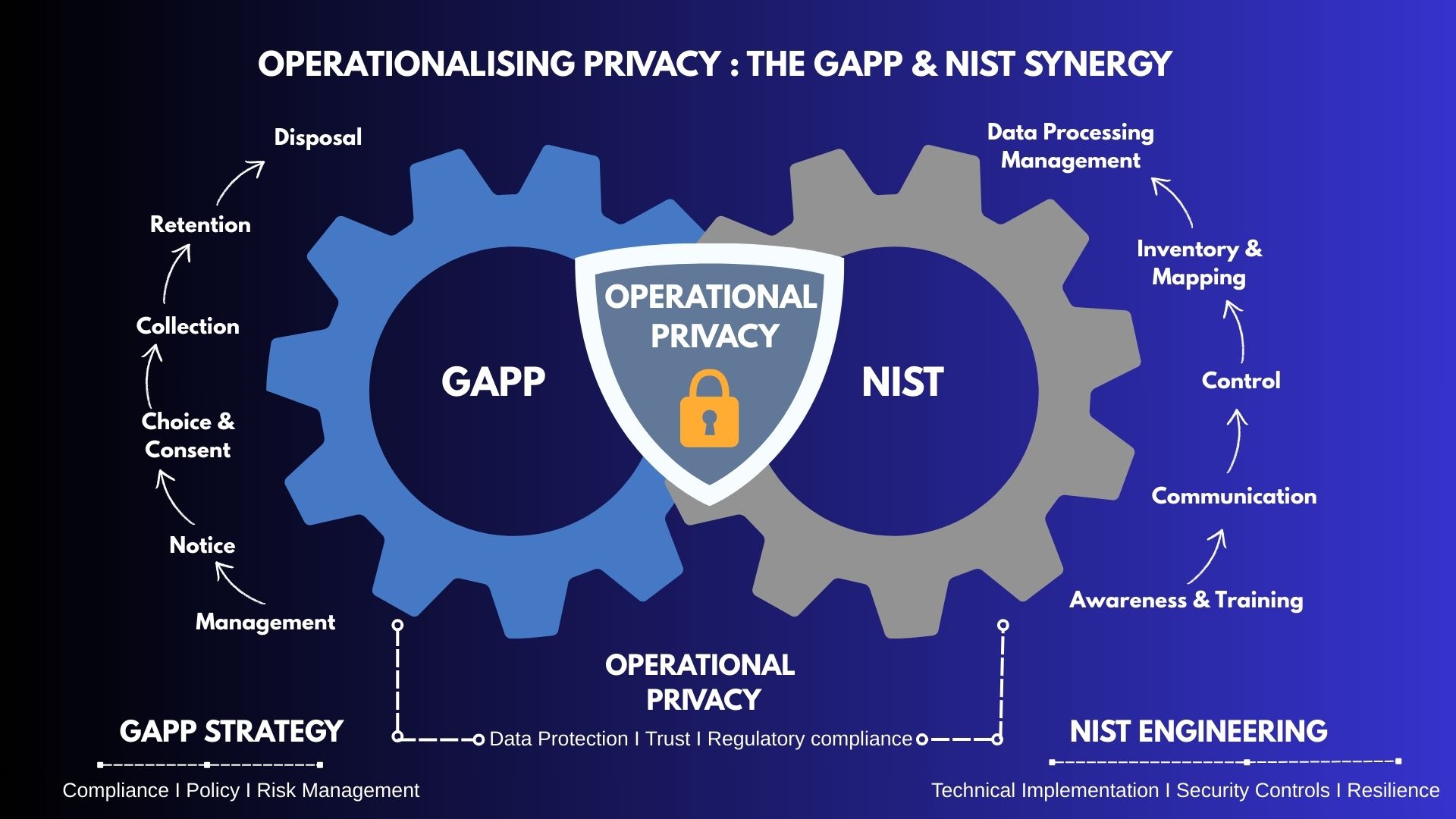
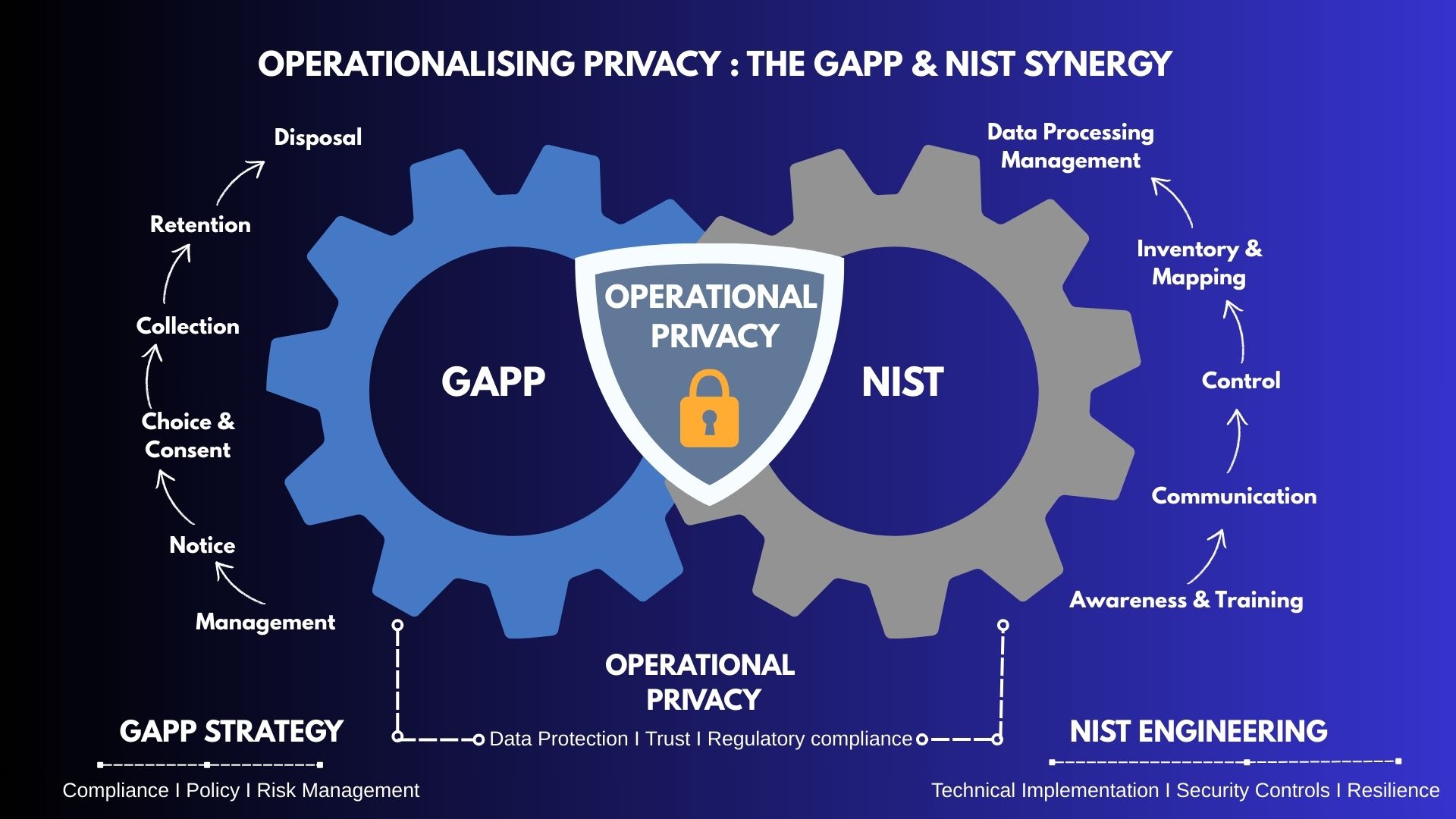
Operationalizing privacy means moving beyond static policies and into a dynamic lifecycle where principles and intent are hardcoded into technical reality. In this first of a two-part series, I will show you how to harmonize the strategic oversight of GAPP with the engineering precision of NIST to transform privacy from a high-level principle into a functional, repeatable, and scalable business process.
To demonstrate this, I will showcase how this harmonized approach is applied to an Antivirus (AV) product. For an AV product, the stakes are unique: the user must trust the software with deep system access to stay safe, but that same access creates a massive privacy footprint. Across these two articles, I will highlight one specific privacy challenge for each GAPP Principle and demonstrate how to technically operationalize the solution using NIST.
Challenge: An AV company requires a large amount of data from a user’s system to catch malware, but it must respect user boundaries. You cannot govern what you cannot see.
Goal: Implement role-based training. Train your malware researchers that while they require samples for analysis, they must strip "Personal Data" before moving those samples into a shared research database. This ensures the "Management" intent is understood by the people actually handling the data.
NIST (GV.AT-P), Awareness and Training: Implement role-based training. Train your malware researchers that while they require samples for analysis, they must strip "Personal Data" before moving those samples into a shared research database. This ensures the "Management" intent is understood by the people actually handling the data.
Challenge: Modern AV products often use Heuristic Analysis in the cloud to look for suspicious behavior using metadata and structural characteristics of files rather than relying solely on a signature database. What if the file name is tax_return_2026.xls or the folder path is C:/user/john/tax? These could contain PII.
Goal: Be honest about what the "Cloud Scan" actually sees. Draft a layered notice specifically for Heuristic Analysis to ensure the user is making an informed choice.
NIST (CM-P), Communication: Implement "In-Product Transparency." When a user enables Heuristic Analysis, explain exactly how their file metadata is processed in the cloud via a real-time notice. For example, use a small info-bubble with sub-text that states: "This feature sends file metadata, hashes, and system IDs to our labs to detect unknown threats. No file content is sent unless a threat is confirmed."
Challenge: The "Community Threat Network," where users submit samples, is what makes modern AV effective. However, this creates significant privacy tension. Users wonder: "If I don’t share my data, am I still safe? If I do share it, can you see my private documents?"
Goal: Be explicit about what data is transferred to the cloud-based threat network and provide a clear "Opt-out" option.
NIST (CT-P), Control: Use NIST CM-P to educate users: "We only submit executable files, never your .docx or .pdf files." Furthermore, if the user chooses to opt out, use NIST’s Control (CT-P) to ensure the upload module is physically disabled at the code level. The backend doesn't just "ignore" the incoming data; the endpoint agent stops sending it entirely.
Challenge: Maximum security often requires maximum data. How do we distinguish between "threat data" and "user data"? The cloud engine needs to know if a process is suspicious, but it does not need to know the identity of the person running it. Collecting machine names (e.g., John-Paul-Laptop) or un-hashed MAC addresses creates a compliance liability with no added value for malware detection.
Goal: Implement Data Minimization by collecting only the specific technical attributes required for detection, not the identity of the user.
NIST (ID.IM-P), Inventory and Mapping: Use NIST 800-60 to perform a rigorous Data Classification exercise to identify Low-Sensitivity Data (e.g., file entropy scores) and High-Sensitivity Data (e.g., installed applications or active network connections). Once classified, use NIST ID.IM-P to audit telemetry data at the source. Implement "Sanitization at the Edge" to scrub or hash PII (like usernames or file paths) before transmission. This is a primary example of Privacy by Design.
Challenge: AV products generate a massive amount of data, including "False Positive" and "Clean" records. Keeping such data indefinitely turns a security tool into a surveillance tool. Additionally, investigations into deep breaches may require "Memory Dumps" containing real-time user activity; storing these indefinitely is a compliance risk and a target for hackers.
Goal: Implement a "Forget by Design" architecture. Ensure data is used only for the specific purpose of threat detection and is destroyed permanently once its analytical value expires.
NIST (CT.DP-P), Data Processing Management: Use NIST CT.DP-P to automate data lifecycle management based on NIST 800-88 sanitization standards.
The Story Doesn't End at Disposal...
We have successfully architected how data enters, resides, and exits the AV system. But how do we handle the "outside world"?
In the next installment, we will dive into the remaining five GAPP principles. We will explore how to manage Third-Party Disclosures without losing control, how to implement "Security for Privacy" using the NIST Cybersecurity Framework, and—most importantly—how to Monitor and Enforce these rules to ensure your privacy program is adaptive and audit-ready.